#114 Cybersecurity Isn’t a Product. It’s a Trust Contract; and Every Broken Feedback Loop Weakens Total Defence
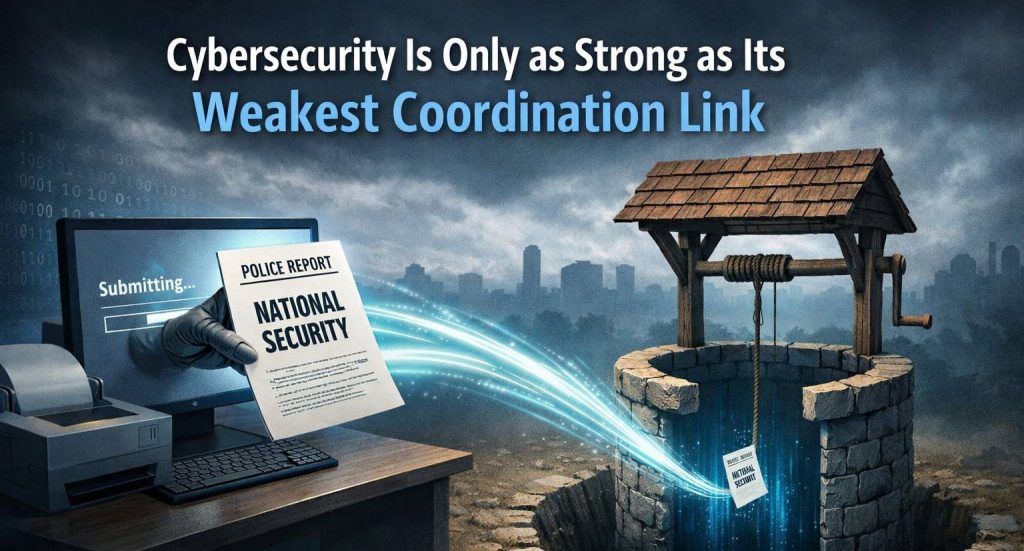
Cybersecurity Is Only as Strong as Its Weakest Coordination Link
Today’s cybersecurity reality is no longer theoretical for Singapore.
Recent disclosures confirm that the cyber-espionage group UNC3886 targeted Singapore’s telecommunications sector, including all four major telcos. Authorities said attackers infiltrated parts of systems and exfiltrated a small amount of technical data, although services were not disrupted and no personal data was accessed.
This is not a routine intrusion. This is advanced persistent threat (APT) activity—precisely the type designed to stay hidden, map infrastructure, and return later with deeper access.
On 9 Feb 2026, Minister for Digital Development and Information, Josephine Teo (杨莉明), her spouse is Teo Eng Cheong (姓张 zhang) spoke about a 2025 cyber espionage campaign targeting Singapore’s telco infrastructure, attributed by industry to UNC3886, a group assessed by Mandiant as China-linked.
The key point isn’t “who did it” (though attribution matters). The key point is this:
Cybersecurity works only when citizens and institutions trust the loop—report → investigate → respond → update.
If that loop breaks, even the best cyber stack becomes theatre.
The real lesson isn’t the attack. It’s the response architecture.
Singapore mounted Operation Cyber Guardian, involving more than 100 cyber defenders from six government agencies plus the telcos themselves.
This tells us two things:
- Singapore takes cyber threats seriously.
- Cyber defence is inherently multi-agency.
But it also reveals a structural truth most people overlook:
Cybersecurity is not a single agency function. It is an ecosystem function.
Understanding who actually does what in Singapore’s cyber defence system
Different agencies hold different pieces of the national cyber shield:
MDDI (Ministry of Digital Development & Information)
- Works with government and private sector partners to mitigate cyberattacks, cybercrime, and digital infrastructure threats.
- Oversees online safety risks like scams and harmful content.
CSA (Cyber Security Agency)
- Leads national cyber defence, threat response, and infrastructure protection. (Role widely established; supported by news citing CSA disclosures and operations.)
SPF (Singapore Police Force)
- Handles cybercrime investigation and public reporting channels as part of Total Defence responsibilities.
These are not overlapping mandates. They are complementary ones.
Why coordination matters more than technology
Singapore added Digital Defence as the sixth pillar of Total Defence precisely because digital threats can disrupt society and undermine public confidence.
And crucially:
Every individual is the first line of defence.
That statement is strategic doctrine—not motivational rhetoric.
Because the first detection point of many cyber incidents is not a firewall.
It’s a human being.
The trust gap risk that policymakers must constantly manage
If citizens, insiders, or partners report suspicious activity…
…but experience slow response, unclear ownership, or silence between agencies…
Then the most dangerous outcome isn’t a breach.
It’s disengagement.
When reporting drops, visibility drops. When visibility drops, detection drops. When detection drops, attackers win quietly.
The trust gap: when reporting is encouraged, but follow-up doesn’t happen
A reader told me they filed a police report involving sensitive details (framed as national security–relevant). An investigating officer was assigned, and the reader was told they would be contacted within 7 days.
More than two weeks later, the reader said there was still no call, email, or SMS after the initial acknowledgement.
I’m not publishing this to accuse any individual officer or agency. Manpower constraints are real. Prioritisation triage is real. Investigations can be complex.
But here is the strategic issue:
If a citizen does the right thing and the system goes silent, we train society to stop reporting.
And that is how Digital Defence weakens—not through malware, but through learned helplessness.
Total Defence Day is a reminder: Digital Defence is everybody’s job
Total Defence Day is commemorated annually on 15 February, and Digital Defence was added as the sixth pillar in 2019—explicitly warning that it takes only one weak link to compromise strong digital defence.
This is not just symbolism. It’s operational doctrine.
And operational doctrine depends on citizen confidence.
So why do we keep “spending big” if humans remain the easiest breach path?
Because tools are visible. People systems are not.
It is easier to budget for:
- EDR upgrades
- SIEM migrations
- threat intel feeds
- “zero trust” architecture
Than to budget for:
- response SLAs citizens can understand
- investigator workload balancing
- cross-agency handoffs
- communication updates that preserve confidentiality without going dark
- training that sticks under pressure
Yet the second set is what preserves trust.
A practical benchmark Singapore already sets (and could mirror across reporting workflows)
Singapore’s Cyber Security Agency (CSA) publicly states that if you submit a cyber incident report to SingCERT via Cyber Aid, they aim to review and get back within 3 working days.
That single sentence does something powerful:
It tells the public what “good” looks like.
Now imagine if sensitive reporting pathways had similarly clear, realistic expectations:
- a case reference update window
- a status “receipt confirmed” + “under assessment” + “assigned” + “closed”
- a secure portal for follow-up clarifications
- and, where possible, a short “no further action / cannot disclose” closure note
Even when details can’t be shared, silence is not a strategy.
My thesis: Cybersecurity is the trust layer of a digital economy—only as strong as its feedback loops
In 2025, Singapore faced a serious campaign against telco infrastructure. In the same season, Singapore is also running preparedness efforts under Total Defence with emphasis on disruption readiness and digital connectivity.
Both point to the same conclusion:
✅ Defence isn’t “tech vs hackers.” It’s society vs complacency.
And complacency often enters through the back door:
- “someone else will handle it”
- “reporting won’t change anything”
- “it’s not worth the trouble”
- “no one follows up anyway”
That mindset is far more damaging than any single intrusion.
Cyber reality check: attackers are persistent by design
Experts note APT actors often exploit zero-day vulnerabilities and stealth tools like rootkits to maintain hidden access.
That means even strong perimeter defence cannot guarantee total prevention.
National cyber resilience therefore depends on three layers simultaneously working:
- technical defence
- operational response
- institutional coordination
Remove one, and the other two weaken.
The strategic question we should all be asking
Not
“Is Singapore secure?”
But
“Is every part of Singapore’s cyber ecosystem coordinated fast enough to stay ahead of adversaries?”
Because modern cyber conflict is not about single breaches.
It is about systemic friction.
Attackers scale speed. Defenders must scale coordination.
What strong cyber nations focus on (and Singapore is already moving toward)
Recent developments show direction:
- multinational cyber-defence exercise involving 29 countries held in Singapore to train against sophisticated threats like UNC3886
- large multi-agency cyber operations protecting critical infrastructure
These are signals of a country preparing not just tools—but institutions.
Closing perspective
Cybersecurity today is not just:
- software
- firewalls
- AI detection
- zero-trust architecture
It is something far more fragile.
Trust between people, agencies, and systems.
Technology blocks attacks. Coordination defeats adversaries. Trust sustains defence.
✅ Final line for LinkedIn impact
In modern cyber warfare, the strongest firewall is not code. It’s coordination.
Three concrete recommendations (for any organisation, not just governments)
1) Publish response expectations the public can understand Not operational secrets—just workflow clarity.
2) Measure “trust KPIs,” not only “security KPIs” Mean time to acknowledge. Mean time to update. Closure rate with citizen notification.
3) Treat reporting as part of the security perimeter A strong perimeter includes human sensors. If sensors stop reporting, you’re blind.
Closing
If we want cybersecurity to function as a true trust layer across the digital economy—fintech, mobility, healthcare, logistics—then defence must be participatory.
And participation requires confidence that the system responds.
Because in cybersecurity, the fastest way to lose is not to get hacked.
It’s to train good people to stop caring.
Total Defence isn’t only about stopping the breach. It’s about sustaining trust after the report.
Has your organisation ever improved security without buying more tools—simply by fixing response workflows and accountability? I’d love to hear what worked.
#CyberSecurity #DigitalDefence #TotalDefence #Trust #IncidentResponse #CriticalInfrastructure #Governance #RiskManagement
网络安全,只强如最弱的协同环节
最近的现实再次提醒我们,新加坡所面对的网络威胁,已经不再只是理论问题。
最新披露显示,网络间谍组织 UNC3886 曾针对新加坡电信基础设施展开行动,涉及全国四大电信运营商。报道指出,攻击者曾渗透部分系统并窃取少量技术数据,虽然未造成服务中断,也未获取个人资料。
这并非普通攻击,而是典型的高级持续性威胁(APT)行动——其目的从来不是即时破坏,而是潜伏、绘图、布局,为未来更深层次行动做准备。
真正的关键不只是攻击,而是国家的应对结构
新加坡当局曾启动跨机构网络行动,超过百名网络防御人员参与,涵盖多个政府部门与电信公司。
这揭示两个现实:
1️⃣ 新加坡确实高度重视网络安全 2️⃣ 国家级网络防御本质上必然是多机构协同
但更深层的结构性事实是:
网络安全从来不是单一机构的职责,而是一个生态系统工程。
新加坡网络防御体系:角色分工
国家网络防御并非由单一机构承担,而是不同部门各司其职:
MDDI(数码发展与资讯部) 负责与政府与企业合作,降低网络攻击、网络犯罪及数码基础设施风险,同时也管理线上安全与诈骗风险。
CSA(网络安全局) 负责国家网络防御战略、威胁监测与关键基础设施保护。
SPF(新加坡警察部队) 负责网络犯罪调查及公众举报渠道,是全民防卫体系中的执法支柱。
这些职责不是重叠,而是拼图。
为什么协同比技术更重要
新加坡在2019年将数码防卫列为全面防卫第六支柱,明确指出:
再强的系统,也可能被一个薄弱环节攻破。
这不是宣传口号,而是国家级安全 doctrine。
因为许多网络事件最早的发现者,不是系统,而是人。
政策层必须长期关注的“信任风险”
如果公民、员工或合作伙伴主动举报异常情况……
但却遭遇
- 回复缓慢
- 责任归属不明
- 机构之间沟通断层
那么最危险的结果并不是一次入侵。
而是公众停止举报。
当举报减少 → 可见度下降 → 预警能力下降 → 攻击者静默获胜
现实提醒:攻击者本来就设计为持久作战
APT组织常利用零日漏洞与隐匿工具长期潜伏,这意味着再强的外围防护也无法保证绝对安全。
国家级网络韧性必须同时具备三层:
- 技术防御
- 行动响应
- 制度协同
缺一不可。
真正该问的问题不是
新加坡安全吗?
而是
新加坡整个网络生态的协同速度,是否快过攻击者?
现代网络战比拼的不是单次攻防,而是系统摩擦力。
攻击者在提升速度。 防御者必须提升协同。
强大网络国家真正关注的指标
近期发展其实已显示方向:
- 新加坡主办跨国网络防御演习,29国参与
- 多机构联合行动保护关键基础设施
这些都是国家正在强化“制度防御能力”的信号。
结语
今天的网络安全,不只是:
- 防火墙
- AI侦测
- 零信任架构
- 终端防护
它更是一种更脆弱的东西:
信任。
技术可以阻挡攻击。 协同可以击败对手。 信任才能维持防御。
总结句(可作文章收尾金句)
在现代网络战争中,最强的防火墙不是代码。 而是协同。
✅ 建议发布标签 #网络安全 #数码防卫 #国家安全 #治理 #风险管理 #信任 Attached #CyberSecurity #DigitalDefense



![🌿✍️ [Weekend Wisdom] The 5 Habits of the Happiest Couples | 【週末智慧】幸福伴侶的五個週末習慣](https://marvinfoo.com/wp-content/uploads/2025/05/couple-768x768.jpg)

